Despite companies using advanced content inspection tools and employee training programs, attacks happen daily. Even AI-powered defense tools struggle to keep up with evolving AI-powered attacks.
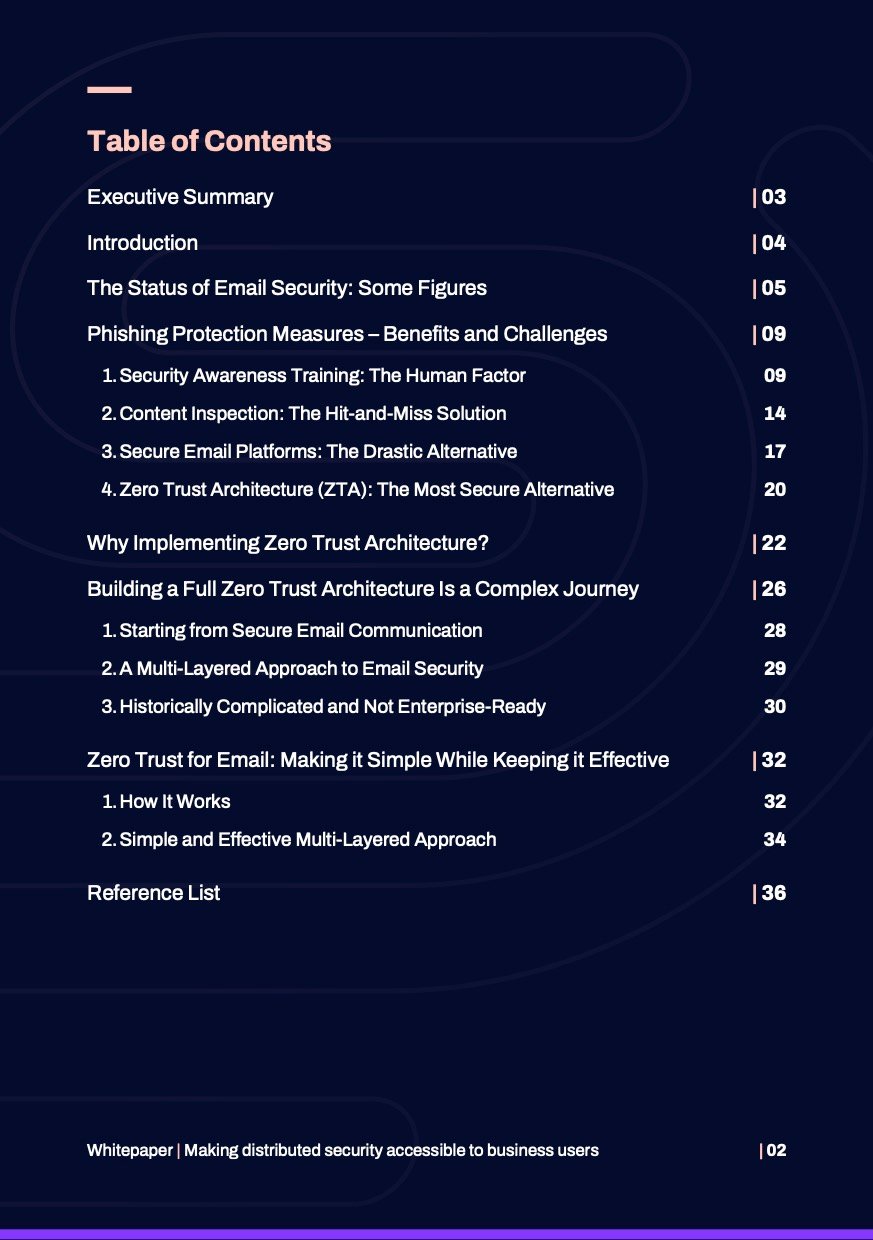
Our whitepaper, written for CISOs, IT decision-makers, and cyber security professionals, analyzes the most common approaches to prevent business email compromise and their shortcomings.
The document describes how implementing a multi-layered approach with Zero Trust email security can minimize the likelihood and effects of a breach. It explains how historical challenges in implementing and using Zero Trust email security can be overcome with robust, reliable, and user-friendly tools.
The future of Zero Trust email security lies in simple and effective solutions that uphold the principles of Zero Trust while keeping costs low and users satisfied.